I was informed a couple of days ago of the Death of my only true best friend. And you might ask why did someone else have to tell me that. And My only answer is that we don’t see or talk to each other all that often.
Me living in Ireland and Larry in Kent Washington (Seattle) IM and email are the only real practical methods. With the time difference we never managed Zoom or Skype. But he was always in my thoughts. We were best geeks you see and if you know what that means, you will understand.
Our live meeting were almost a catch up competition of who was doing what, with whatever new thing that was going on. More often than not we were on the same technology page.
Matters or life and death or even politics didn’t even rise to the level of mention. And were not missed. The future was bright, and we were immortal.
30 years we could call our friendship having been brought together on a project at Battelle’s Pacific Northwest National Lab. On a project that as far as I know continues to operate there, the NIB.
During that time, we operated often in separate areas and in different companies. But always connected in some way. Even our Dogs were best friends. Larry never did forgive me for teaching his Charlie to bark.
He will be missed my many, and I am among them. The world is a lesser place.
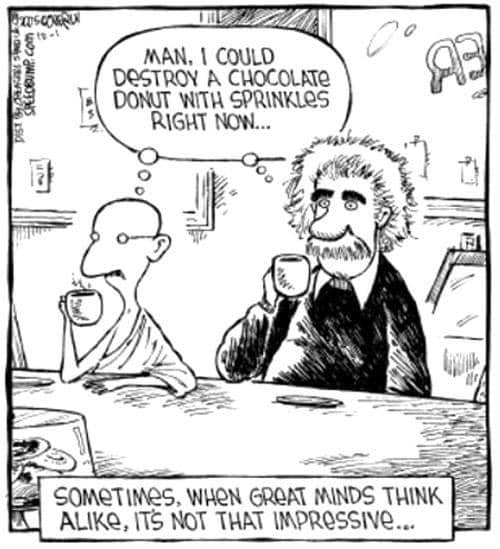
I was trying to imagine a funny joke, or a photo that would evoke the two of us, and stumbled upon this one. And it suites, even our self defined importance in the world.
I hope you enjoy it.
Bugs I’ll miss you.
Randy.